Summary
Worm:W32/Yaha.E spreads as an attachment with different names in email messages with different subjects and bodies, the message composition routine is really complex.
Removal
Based on the settings of your F-Secure security product, it will either move the file to the quarantine where it cannot spread or cause harm, or remove it.
A False Positive is when a file is incorrectly detected as harmful, usually because its code or behavior resembles known harmful programs. A False Positive will usually be fixed in a subsequent database update without any action needed on your part. If you wish, you may also:
Check for the latest database updates
First, check if your F-Secure security program is using the latest updates, then try scanning the file again.
Submit a sample
After checking, if you still believe the file is incorrectly detected, you can submit a sample of it for re-analysis.
Note: If the file was moved to quarantine, you need to collect the file from quarantine before you can submit it.
Exclude a file from further scanning
If you are certain that the file is safe and want to continue using it, you can exclude it from further scanning by the F-Secure security product.
Note: You need administrative rights to change the settings.
Technical Details
The worm's file is a Windows PE (portable executable) file about 27 kb long. The file is packed with UPX file compressor and UPX text strings in the body of the worm are replaced with dots probably by the worm's author.
Worm's files usually have random data (garbage) in the end, the length and content of that area is different in different samples. The worm has most of its text strings encrypted with a simple crypto algorithm.
Yaha.E worm became widespread on 20th of June 2002. The worm was reported from several different countries.
Installation
The worm usually installs itself with random name to C:\Recycler or C:\Recycled folder or, if these folders are not available, into Windows directory.
The worm then modifies default EXE file startup key to make itself run every time an EXE program is started.
- [HKCR\exefile\shell\open\command]
Also one of the threads of the worm continuously refreshes this key to prevent its modification by computer user or by disinfection utility. The same thread tries to kill Windows Task Manager process.
The worm creates a file named KITKAT in a temporary folder and writes its BASE64-encoded file data there. That file will be different from the original worm sample as the worm adds random data to its end (from MUNCH file that it generates and then deletes). The length of random data area differs every time. This technique was supposed to fool some anti-virus scanners that use CRC to detect standalone malware.
The worm doesn't start when launched from Internet Explorer cache folder (folder containing CONTENT.IE5 string). If the worm is started from MSTASKMON.EXE file, it adds execution string for this file into WIN.INI to be started every time Windows runs. The worm starts itself as a service process, so its task is not visible in Task Manager under Windows 9x systems.
Activity
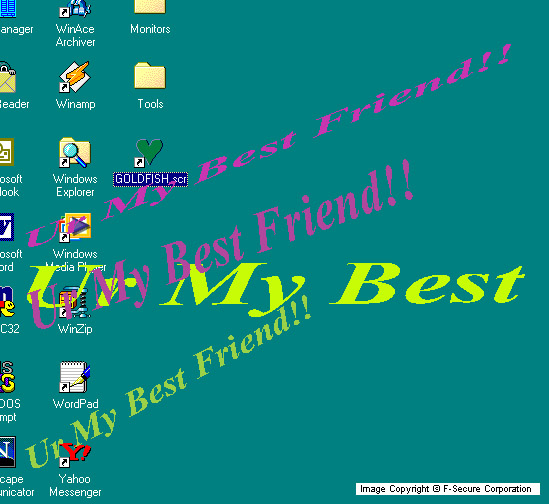
When the worm's file is started on a clean system and its file has SCR extension, it may display a messagebox or/and a videoeffect. The effect will look like that (the screen will be shaking):
One of worm's threads from time to time tries to connect to a 'www.pak.gov.pk' website (possibly related to the Pakistanian government). If the worm is widespread, this can cause a DoS (Denial of Service) attack on that webserver.
The worm looks for and terminates the processes that have the following strings in their names:
- PCCIOMON
- PCCMAIN
- POP3TRAP
- WEBTRAP
- AVCONSOL
- AVSYNMGR
- VSHWIN32
- VSSTAT
- NAVAPW32
- NAVW32
- NMAIN
- LUALL
- LUCOMSERVER
- IAMAPP
- ATRACK
- NISSERV
- RESCUE32
- SYMPROXYSVC
- NISUM
- NAVAPSVC
- NAVLU32
- NAVRUNR
- NAVWNT
- PVIEW95
- F-STOPW
- F-PROT95
- PCCWIN98
- IOMON98
- FP-WIN
- NVC95
- NORTON
- MCAFEE
- ANTIVIR
- WEBSCANX
- SAFEWEB
- ICMON
- CFINET
- CFINET32
- AVP.EXE
- LOCKDOWN2000
- AVP32
- ZONEALARM
- WINK
- SIRC32
- SCAM32
So the worm not only kills tasks of anti-virus and security software, it also kills tasks of Klez and Sircam worms. The worm has different process killing routines for different types of operating systems. The worm doesn't allow programs with the above mentioned strings in their names to start on an infected system. The worm also looks for and terminates the Windows Task Manager process.
The worm creates the TXT file with random name in Windows directory with the following text:
iNDian sNakes pResents yAha.E iNDian hACkers,Vxers c0me & w0Rk wITh uS & f*Ck tHE GFORCE-pAK sh*tes bY sNAkeeYes,c0Bra
Propagation (email)
The worm loads Windows Address Book into memory, reads .NET Messenger data, Yahoo! Messenger profiles, ICQ data files, HTML, DOC and TXT files in cache folders, desktop and personal folders and stores email addresses it could find there into a DLL file with a random name in Windows folder.
The worm uses a set of pre-defined smtp server names, message bodies, subjects, attachment names and extensions and selects them randomly to compose an email message that it will send to all found email addresses. It can send different types of emails, similar to Klez worms emails. The worm may or may not include IFrame exploit into the message that it sends out.
The subject of infected email can be one of the following messages or a combination of them:
- searching for true Love
- you care ur friend
- Who is ur Best Friend
- make ur friend happy
- True Love
- Dont wait for long time
- Free Screen saver
- Friendship Screen saver
- Looking for Friendship
- Need a friend?
- Find a good friend
- Best Friends
- I am For u
- Life for enjoyment
- Nothink to worryy
- Ur My Best Friend
- Say 'I Like You' To ur friend
- Easy Way to revel ur love
- Wowwwwwwwwwww check it
- Send This to everybody u like
- Enjoy Romantic life
- Let's Dance and forget pains
- war Againest Loneliness
- How sweet this Screen saver
- Let's Laugh
- One Way to Love
- Learn How To Love
- Are you looking for Love
- love speaks from the heart
- Enjoy friendship
- Shake it baby
- Shake ur friends
- One Hackers Love
- Origin of Friendship
- The world of lovers
- The world of Friendship
- Check ur friends Circle
- Friendship
- how are you
- U r the person?
- U realy Want this
Also the worm can compose the subject from 2 or more different parts with or without 'Fw:' prefix:
- Romantic
- humour
- NewWonderfool
- excite
- Cool
- charming
- Idiot
- Nice
- Bullsh*t
- One
- Funny
- Great
- LoveGangs
- Shaking
- powful
- Joke
- Interesting
- Screensaver
- Friendship
- Love
- relations
- stuff
- to ur friends
- to ur lovers
- for you
- to see
- to check
- to watch
- to enjoy
- to share
- :-)
- !
- !!
For example the subject of an infected message can be 'Cool stuff to see' or 'FW: Nice Screensaver for you !!'. There can be 'Fw:' prefix to the subject.
The infected message body can contain one of the following strings or blocks of strings:
- Check the attachment
- See the attachement
- Enjoy the attachement
- More details attached
- Hi Check the Attachement .. See u
- Hi Check the Attachement .. Attached one Gift for u.. wOW CHECK THIS
Then there can follow a fake undeliverable message report or a fake screensaver subscription message. In case the worm sends a fake bounced message, it looks like that:
This message was created automatically by mail delivery software (Exim). A message that you sent could not be delivered to one or more of its recipients. This is a permanent error. The following address(es) failed: [sender's email address]For further assistance, please contact [postmaster's email address] If you do so, please include this problem report. You can delete your own text from the message returned below. Copy of your message, including all the headers is attached
Then there goes an EML file attachment with random name that contains the worm's sample and usually IFrame exploit to make the attachment run automatically on unpatched email clients.
In case the worm spreads itself with a fake screensaver subscription message, it looks like that:
This email is never sent unsolicited. If you need to unsubscribe, follow the instructions at the bottom of the message.***********************************************************Enjoy this friendship Screen Saver and Check ur friends circle... Send this screensaver from [constructed URL] to everyone you consider a FRIEND, even if it means sending it back to the person who sent it to you. If it comes back to you, then you'll know you have a circle of friends. * To remove yourself from this mailing list, point your browser to:[constructed URL] * Enter your email address ([sender's email address]) in the field provided and click "Unsubscribe". OR... * Reply to this message with the word "REMOVE" in the subject line. This message was sent to address [sender's email address] X-PMG-Recipient: [sender's email address]
In this case the worm spreads itself with one of the below given names and only SCR extension:
- screensaver
- screensaver4u
- screensaver4u
- screensaverforu
- freescreensaver
- love
- lovers
- lovescr
- loverscreensaver
- loversgang
- loveshore
- love4u
- lovers
- enjoylove
- sharelove
- shareit
- checkfriends
- urfriend
- friendscircle
- friendship
- friends
- friendscr
- friends
- friends4u
- friendship4u
- friendshipbird
- friendshipforu
- friendsworld
- werfriends
- passion
- bullshitscr
- shakeit
- shakescr
- shakinglove
- shakingfriendship
- passionup
- rishtha
- greetings
- lovegreetings
- friendsgreetings
- friendsearch
- lovefinder
- truefriends
- truelovers
- f*cker
The worm also spreads itself as an attachment with double extension and with one of the following names or with a random name:
- loveletter
- resume
- biodata
- dailyreport
- mountan
- goldfish
- weeklyreport
- report
- love
The first extension of the attachment can be:
- doc
- mp3
- xls
- wav
- txt
- jpg
- gif
- dat
- bmp
- htm
- mpg
- mdb
- zip
The second (last) extension of the infected attachment can be:
- pif
- bat
- scr
For example the worm's attachment name can be GOLDFISH.MPG.PIF or BIODATA.DOC.SCR. The attachment content type that the worm uses can be one of the following:
- audio/x-midi
- audio/x-wav
Propagation (Local Area Network)
The worm has network spreading capabilities. One of the threads constantly looks for open shares and searches directories with the following names there:
- WINXP
- WINME
- WIN
- WINNT
- WIN95
- WIN98
- WINDOWS
When the worm finds a directory with any of the above mentioned names, it tries to find WIN.INI file in that directory. If it can find such a file, the worm copies itself as MSTASKMON.EXE file into the same directory and modifies WIN.INI file on remote system to start itself there after next reboot.
It should be noted that this functionality will only work under Windows 9x systems as WIN.INI file is not used by NT-based systems. But the worm can be activated on remote NT-based system if a user runs MSTASKMON.EXE file there.
Protect your devices from malware with F‑Secure Total
Protecting your devices from malicious software is essential for maintaining online security. F‑Secure Total makes this easy, helping you to secure your devices in a brilliantly simple way.
Award‑winning antivirus and malware protection
Online browsing, banking, and shopping protection
24/7 online identity and data breach monitoring
Unlimited VPN service to safeguard your privacy
Password manager with private data protection
Choose how many devices you want to protect to get started.
Free customer support
Cancel anytime
The trial does not obligate you to buy the product
After 30 days your subscription will renew automatically for one year at €69.99.
More Support
Community
Ask questions in our Community.
User guides
Check the user guide for instructions.
Contact Support
Chat with with or call an agent.
Submit a Sample
Submit a file or URL for analysis.


)
)