Summary
Trojan.GenericKD.2427119 appears to be a ZIP file containing a PDF document, but when extracted, the contained file is an executable program that silently connects to remote servers to download files onto the infected machine. During the analysis, one of the downloaded files attempted to use the machine to send spam email messages.
Removal
Based on the settings of your F-Secure security product, it will either move the file to the quarantine where it cannot spread or cause harm, or remove it.
A False Positive is when a file is incorrectly detected as harmful, usually because its code or behavior resembles known harmful programs. A False Positive will usually be fixed in a subsequent database update without any action needed on your part. If you wish, you may also:
Check for the latest database updates
First, check if your F-Secure security program is using the latest updates, then try scanning the file again.
Submit a sample
After checking, if you still believe the file is incorrectly detected, you can submit a sample of it for re-analysis.
Note: If the file was moved to quarantine, you need to collect the file from quarantine before you can submit it.
Exclude a file from further scanning
If you are certain that the file is safe and want to continue using it, you can exclude it from further scanning by the F-Secure security product.
Note: You need administrative rights to change the settings.
Technical Details
This malware (SHA1: e81a329b75e962ebef17faf72f2b7d4d0f391589) is distributed from a malicious website in a ZIP file with the filename 'DHL_Report_[string of numbers].zip'. The ZIP file appears to contain a PDF document, as the file uses the PDF file format icon.
Execution
On extraction, the file contained in the ZIP file turns out to be an executable program. When this file is executed, it appears to be damaged and displays an error message:
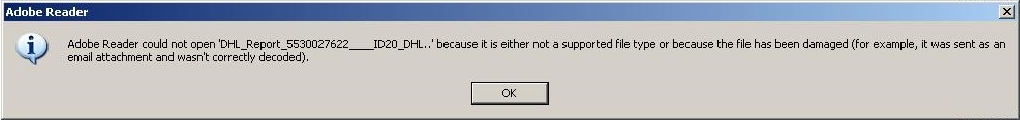
Decoy error message displayed
In the background however, the program injects code into running processes (including explorer.exe).
It also silently attempts to connect to remote servers (mainly located in the United States, United Kingdom and Japan).
Files downloaded
On successfully connecting to the remote servers, it downloads files and saves them on the machine. A file is saved to the user profile and uses the PDF file format to help conceal the fact that the file is actually an executable program:
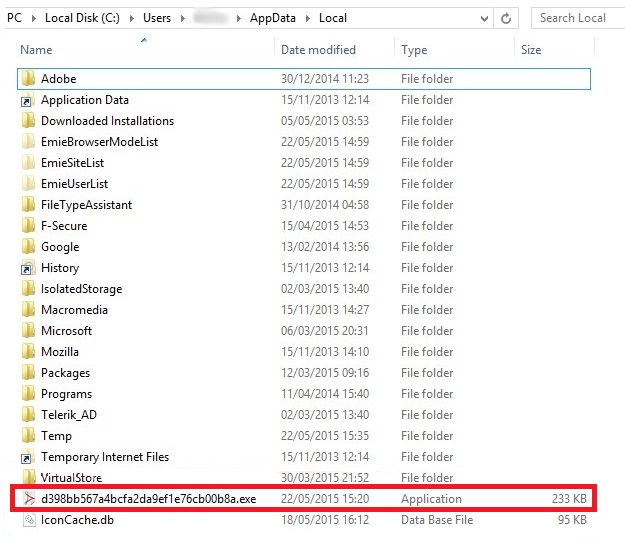
File downloaded to the user profile
The malware then amends the registry so that this file is automatically run on system startup.
In addition, innocuously named files (for example, '25.tmp') are saved to the temp folder:
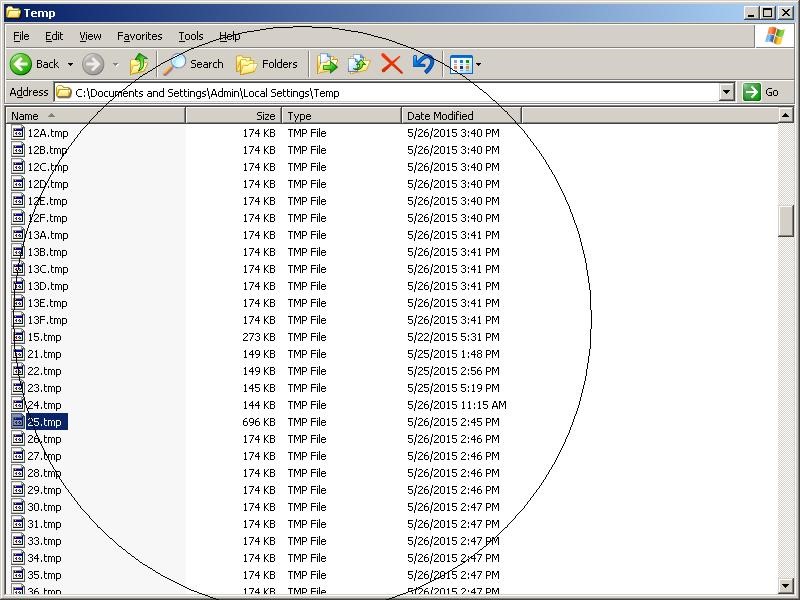
Files downloaded to the temp folder
Proxy server changes
In the registry, the trojan changes the settings for the proxy server to the local address. It also modifies the proxy settings in the Internet Explorer web browser's Local Area Network (LAN) settings.
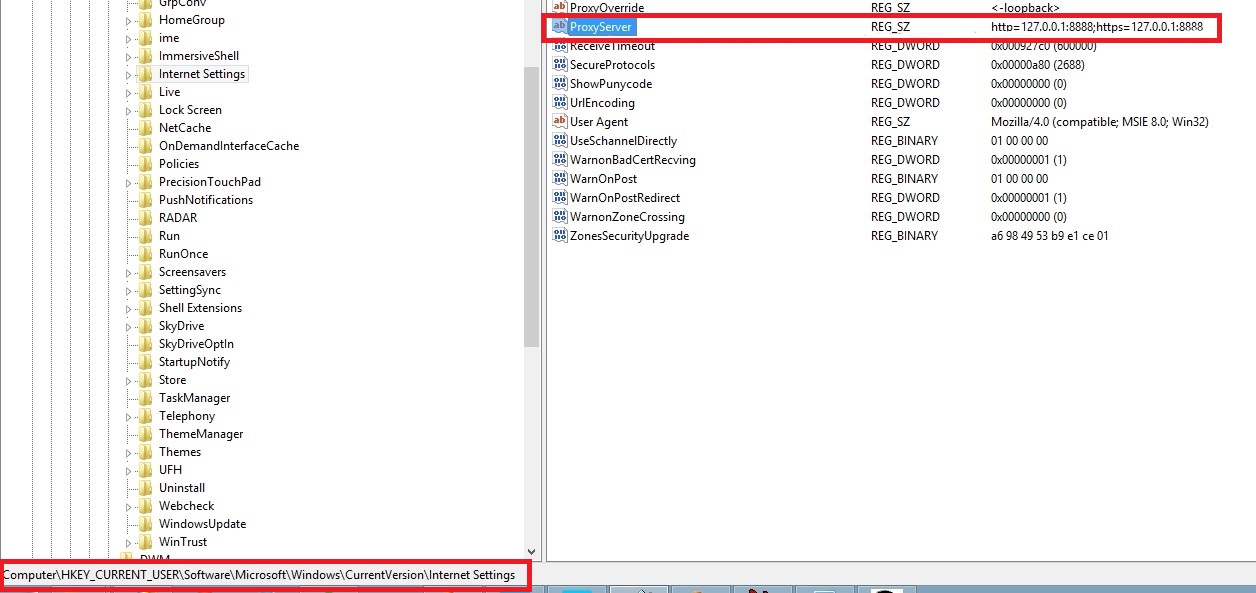
Proxy setting changes for Internet Settings
These changes typically interfere with the user's normal connection to the Internet.
Sending spam
During the analysis, the 25.tmp file was observed to be a self-extracting executable program that attempts to connect to various SMTP servers:
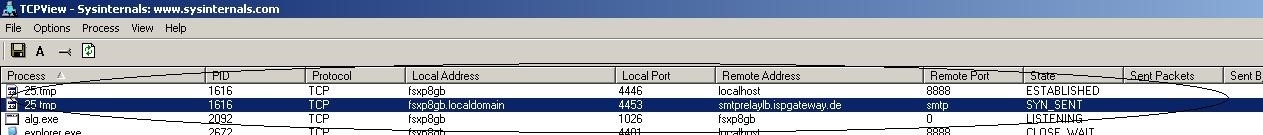
25.tmp attempting to contact an SMTP server
If successfully connected, the program begins sending spam email messages to a list of recipient email addresses that it also downloaded from the remote servers:
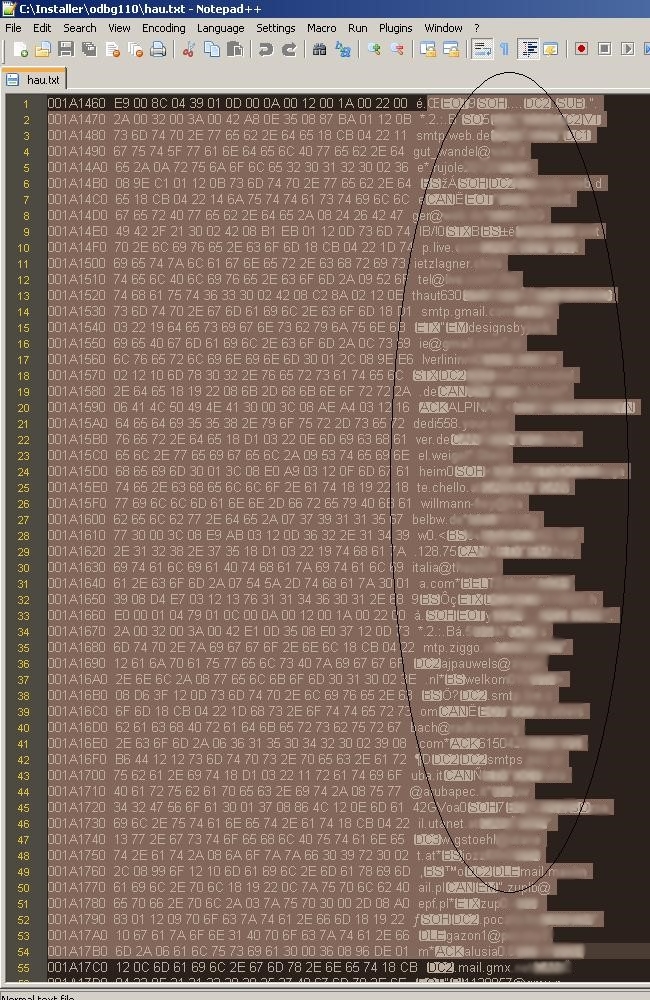
Spam email message recipients list
Protect your devices from malware with F‑Secure Total
Protecting your devices from malicious software is essential for maintaining online security. F‑Secure Total makes this easy, helping you to secure your devices in a brilliantly simple way.
Award‑winning antivirus and malware protection
Online browsing, banking, and shopping protection
24/7 online identity and data breach monitoring
Unlimited VPN service to safeguard your privacy
Password manager with private data protection
Choose how many devices you want to protect to get started.
Free customer support
Cancel anytime
The trial does not obligate you to buy the product
After 30 days your subscription will renew automatically for one year at €69.99.
More Support
Community
Ask questions in our Community.
User guides
Check the user guide for instructions.
Contact Support
Chat with with or call an agent.
Submit a Sample
Submit a file or URL for analysis.


)
)