Summary
This new version of the Klez worm has been found from various parts of Asia on April 17th, 2002. A week after its discovery Klez.H is globally spread. This worm, like its previous versions sends email messages with randomly named attachments and subject fields.
Removal
Based on the settings of your F-Secure security product, it will either move the file to the quarantine where it cannot spread or cause harm, or remove it.
We have produced a video showing step-by-step how to get rid of the Klez worm. View the video at: http://www.f-secure.com/virus-info/video/klez.ram
Note: The video requires RealPlayer to view. You may download RealPlayer from: http://www.real.com/player/index.html?lang=en
A False Positive is when a file is incorrectly detected as harmful, usually because its code or behavior resembles known harmful programs. A False Positive will usually be fixed in a subsequent database update without any action needed on your part. If you wish, you may also:
Check for the latest database updates
First, check if your F-Secure security program is using the latest updates, then try scanning the file again.
Submit a sample
After checking, if you still believe the file is incorrectly detected, you can submit a sample of it for re-analysis.
Note: If the file was moved to quarantine, you need to collect the file from quarantine before you can submit it.
Exclude a file from further scanning
If you are certain that the file is safe and want to continue using it, you can exclude it from further scanning by the F-Secure security product.
Note: You need administrative rights to change the settings.
Technical Details
The Klez.H variant it quite close to previous variants Klez.E, F and G.
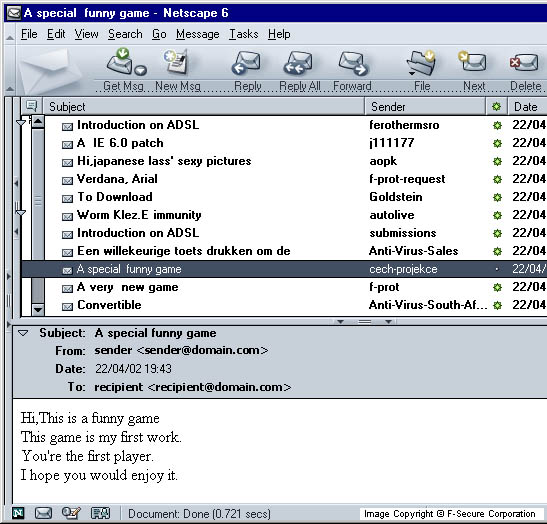
Here is a screenshot showing what Klez messages could look like:
F-Secure Virus Research Team found the following differences in Klez.H variant compared to its previous versions:
- There's no payload routine.
- The .PDF extension was added to the list of extensions that the worm uses to make a double-extension name for its file.
- The worm sometimes uses social engineering approach in its spreading and sends the following message with its own file attached : Subject: Worm Klez.E immunity Body: Klez.E is the most common world-wide spreading worm.It's very dangerous by corrupting your files. Because of its very smart stealth and anti-anti-virus technic,most common AV software can't detect or clean it. We developed this free immunity tool to defeat the malicious virus. You only need to run this tool once,and then Klez will never come into your PC. NOTE: Because this tool acts as a fake Klez to fool the real worm,some AV monitor maybe cry when you run it. If so,Ignore the warning,and select 'continue'. If you have any question,please mail to me. The 'mail to me' is represented as a link to the sender's email address. Note that this address is not always the real sender's address.
- The worm contains a new text message from its author. This text is never displayed: Win32 Klez V2.01 & Win32 Foroux V1.0 Copyright 2002,made in Asia About Klez V2.01: 1,Main mission is to release the new baby PE virus,Win32 Foroux 2,No significant change.No bug fixed.No any payload. About Win32 Foroux (plz keep the name,thanx) 1,Full compatible Win32 PE virus on Win9X/2K/NT/XP' 2,With very interesting feature.Check it! 3,No any payload.No any optimization' 4,Not bug free,because of a hurry work.No more than three weeks from having such idea to accomplishing coding and testing'
- The worm drops an Elkern variant. Unlike the previous Klez versions, Klez.H puts the virus dropper into \Program Files\ folder with a random name and activates it.
- The worm added 2 more names to the list of anti-virus companies that it previously had. These new names are:
- The latest Klez variants, including Klez.H, can send out user's files with its message. The worm can randomly pick a file with one of the following extensions and attach it to its infected message:
Protect your devices from malware with F‑Secure Total
Protecting your devices from malicious software is essential for maintaining online security. F‑Secure Total makes this easy, helping you to secure your devices in a brilliantly simple way.
Award‑winning antivirus and malware protection
Online browsing, banking, and shopping protection
24/7 online identity and data breach monitoring
Unlimited VPN service to safeguard your privacy
Password manager with private data protection
Choose how many devices you want to protect to get started.
Free customer support
Cancel anytime
The trial does not obligate you to buy the product
After 30 days your subscription will renew automatically for one year at €69.99.
More Support
Community
Ask questions in our Community.
User guides
Check the user guide for instructions.
Contact Support
Chat with with or call an agent.
Submit a Sample
Submit a file or URL for analysis.


)
)