Summary
The Sober.X worm was found on November 15th, 2005. This Sober variant is similar to Sober.T, that appeared yesterday:
https://www.f-secure.com/v-descs/sober-t
Like the previous variants, this one sends itself inside a ZIP archive as an attachment in email messages with English or German texts. We also received several different droppers for this worm variant. They were apparently created by the worm author manually. They are all detected as 'Sober.x'.
Removal
Based on the settings of your F-Secure security product, it will either move the file to the quarantine where it cannot spread or cause harm, or remove it.
A False Positive is when a file is incorrectly detected as harmful, usually because its code or behavior resembles known harmful programs. A False Positive will usually be fixed in a subsequent database update without any action needed on your part. If you wish, you may also:
Check for the latest database updates
First, check if your F-Secure security program is using the latest updates, then try scanning the file again.
Submit a sample
After checking, if you still believe the file is incorrectly detected, you can submit a sample of it for re-analysis.
Note: If the file was moved to quarantine, you need to collect the file from quarantine before you can submit it.
Exclude a file from further scanning
If you are certain that the file is safe and want to continue using it, you can exclude it from further scanning by the F-Secure security product.
Note: You need administrative rights to change the settings.
Technical Details
Sober.Y is written in Visual Basic. The worm's file is a UPX packed PE executable about 55 kilobytes long. The unpacked worm's file size is around 198 kilobytes.
This time the author of Sober worm changed the text string that is used to decrypt data strings in the worm's body, but he did not change the encryption algorithm.
Installation
Just after being run by a user the worm shows a fake error messagebox:
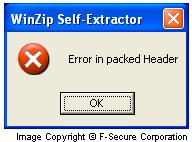
Then it creates a subfolder named 'WinSecurity' in Windows folder and copies itself there 3 times with the following names:
- services.exe
- csrss.exe
- smss.exe
In addition the worm creates the following files in the same folder:
- mssock1.dli
- mssock2.dli
- mssock3.dli
- winmem1.ory
- winmem2.ory
- winmem3.ory
- socket1.ifo
- socket2.ifo
- socket3.ifo
The first 6 files are used to store collected email addresses, the last 3 files are used to store the UUEncoded worm's body.
The worm then adds startup keys for the copied "services.exe" file into System Registry:
- [HKLM\Software\Microsoft\Windows\CurrentVersion\Run] " Windows" = "%WinDir%\WinSecurity\services.exe"
- [HKCU\Software\Microsoft\Windows\CurrentVersion\Run] "_Windows" = "%WinDir%\WinSecurity\services.exe"
The Sober.Y worm creates a few empty files in Windows System folder with the following names:
- nonrunso.ber
- langeinf.lin
- runstop.rst
- rubezahl.rub
- bbvmwxxf.hml
- filesms.fms
These files are used to deactivate previous Sober variants. The worm blocks access to its files and re-creates its startup keys in the Registry if they are deleted.
To collect email addresses the worm scans files with the following extensions:
Pmr phtm stm slk inbox imb csv bak imh xhtml imm imh cms nws vcf ctl dhtm cgi pp ppt msg jsp oft vbs uin ldb abc pst cfg mdw mbx mdx mda adp nab fdb vap dsp ade sln dsw mde frm bas adr cls ini ldif log mdb xml wsh tbb abx abd adb pl rtf mmf doc ods nch xls nsf txt wab eml hlp mht nfo php asp shtml dbx The collected email addresses are stored in "mssock*.dli" and "winmem*.ory" files that are created in the same folder where the main worm's executable file is located.
The worm ignores email addresses if they contain any of the following strings:
ntp- ntp@ ntp. test@ @www @from. support smtp- @smtp.
Gold-certs ftp. .dial. .ppp. anyone subscribe announce @gmetref sql. someone nothing you@ user@ reciver@ somebody secure whatever@ whoever@ anywhere yourname mustermann@ .kundenserver. mailer-daemon variabel noreply -dav law2 .sul.t- .qmail@ t-ipconnect t-dialin ipt.aol time freeav @ca. abuse winrar domain. host. viren bitdefender spybot detection ewido. emsisoft linux google @foo. winzip @example. bellcore. @arin mozilla iana@ iana- @iana @avp icrosoft. @sophos @panda @kaspers free-av antivir virus verizon. @ikarus. @nai. @messagelab nlpmail01. clock When the worm sends an email to an address that contains "gmx." domain or has the domain suffix ".de", ".li", ".ch" or ".at", it composes messages in German, otherwise the worm composes messages in English.
It should be noted that along with the "usual" messages that look like fake bounces, password change notifications, Paris Hilton video ads and so on, the worm sends messages that look like they come from FBI or CIA. The From field of such messages contains any of the following:
- Department@fbi.gov (also can be Office@, Admin@, Mail@, Post@)
- Department@cia.gov (also can be Office@, Admin@, Mail@, Post@)
The Subject field contains any of the following:
- You visit illegal websites
- Your IP was logged
The body text is:
Dear Sir/Madam, we have logged your IP-address on more than 30 illegal Websites. Important:Please answer our questions! The list of questions are attached. Yours faithfully, Steven Allison *** Federal Bureau of Investigation -FBI- *** 935 Pennsylvania Avenue, NW, Room 3220 *** Washington, DC 20535 *** phone: (202) 324-3000
If the worm uses @cia.gov address, the end of the message is different:
- ++++ Central Intelligence Agency -CIA-
- ++++ Office of Public Affairs
- ++++ Washington, D.C. 20505
- ++++ phone: (703) 482-0623
- ++++ 7:00 a.m. to 5:00 p.m., US Eastern time
The attachment names can be:
- question_list.zip
- list.zip
The similar message in German, but this time from BKA. The From field of such messages contains any of the following:
- Downloads@bka.bund.de (also can be BKA@, Internet@, Post@, Anzeige@, BKA.Bund@)
The Subject field contains any of the following:
- Ermittlungsverfahren wurde eingeleitet
- Sie besitzen Raubkopien
The body text is:
Sehr geehrte Dame, sehr geehrter Herr, das Herunterladen von Filmen, Software und MP3s ist illegal und somit strafbar. Wir moechten Ihnen hiermit vorab mitteilen, dass Ihr Rechner unter der IP erfasst wurde. Der Inhalt Ihres Rechner wurde als Beweismittel sichergestellt und es wird ein Ermittlungsverfahren gegen Sie eingleitet. Die Strafanzeige und die Moeglichkeit zur Stellungnahme wird Ihnen in den naechsten Tagen schriftlich zugestellt. Aktenzeichen NR.:# (siehe Anhang) Hochachtungsvoll i.A. Juergen Stock --- Bundeskriminalamt BKA --- Referat LS 2 --- 65173 Wiesbaden --- Tel.: +49 (0)611 - 55 - 12331 oder --- Tel.: +49 (0)611 - 55 - 0
The attachment name can be:
- Akte.zip
Here's an example of a message sent by the worm:
The worm's executable file is located inside ZIP archives attached to all infected messages. To get infected a user has to extract and run the worm's file.
- microsoftanti
- gcas
- gcip
- giantanti
- inetupd.
- nod32kui
- nod32.
- fxsbr
- avwin.
- guardgui.
- aswclnr
- stinger
- hijack
- sober
- brfix
- s_t_i_n
- s-t-i-n
Then the worm shows a messagebox that looks like that:
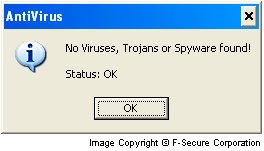
This trick is done to persuade a user that no infection was detected on his computer by his anti-virus or a virus removal tool.
The worm can also download and run files on an infected computer.
In addition the worm contacts numerous time servers to syncronize its activities.
Protect your devices from malware with F‑Secure Total
Protecting your devices from malicious software is essential for maintaining online security. F‑Secure Total makes this easy, helping you to secure your devices in a brilliantly simple way.
Award‑winning antivirus and malware protection
Online browsing, banking, and shopping protection
24/7 online identity and data breach monitoring
Unlimited VPN service to safeguard your privacy
Password manager with private data protection
Choose how many devices you want to protect to get started.
Free customer support
Cancel anytime
The trial does not obligate you to buy the product
After 30 days your subscription will renew automatically for one year at €69.99.
More Support
Community
Ask questions in our Community.
User guides
Check the user guide for instructions.
Contact Support
Chat with with or call an agent.
Submit a Sample
Submit a file or URL for analysis.


)
)