Worm:W32/Zimuse.B
Summary
Zimuse is a family of worms that performs destructive overwrite of the Master Boot Record of disk drives on the infected system.
Removal
Based on the settings of your F-Secure security product, it will either move the file to the quarantine where it cannot spread or cause harm, or remove it.
A False Positive is when a file is incorrectly detected as harmful, usually because its code or behavior resembles known harmful programs. A False Positive will usually be fixed in a subsequent database update without any action needed on your part. If you wish, you may also:
-
Check for the latest database updates
First check if your F-Secure security program is using the latest updates, then try scanning the file again.
-
Submit a sample
After checking, if you still believe the file is incorrectly detected, you can submit a sample of it for re-analysis.
Note: If the file was moved to quarantine, you need to collect the file from quarantine before you can submit it.
-
Exclude a file from further scanning
If you are certain that the file is safe and want to continue using it, you can exclude it from further scanning by the F-Secure security product.
Note: You need administrative rights to change the settings.
Technical Details
Arrival to the system
Zimuse.B arrives on the system either as a standalone file (possibly from a malicious download or email) or by infected removable devices (e.g., USB sticks).
When the malware is executed, it will install malicious components along with a clean IQTest program and a readme.txt. The Iqtest.exe program is clean and is an actual IQ test program.
The following file operations will be performed on the system:
-
Creates these files:
- %windir%\system32\drivers\Mstart.sys [Worm.Zimuse.A]
- %programfiles%\Dump\Dump.exe [nonmalicious component]
- %windir%\system32\drivers\Mseu.sys [Worm.Zimuse.A]
- %windir%\system32\mseus.exe [Worm.Zimuse.A]
- %windir%\system32\tokset.dll [copy of itself]
- %windir%\system32\ainf.inf [copy of the autorun.inf file]
- c:\IQTEST\Iqtest.exe [clean IQTest program]
- c:\IQTEST\Readme.txt [clean text file]
-
Uses these temporary files:
- %temp%\Regini.exe
- %temp%\Dump.ini
- %temp%\Mseu.ini
- %temp%\mseus.ini
- %temp%\Instdrv.exe
Launchpoint/Autostart
Uses registry launchpoints to ensure its components run or are loaded as services on every startup (see below).
Registry Changes
Creates these keys:
- HKLM\System\CurrentControlSet\Services\EventLog\System\MSTART
- HKLM\System\CurrentControlSet\Services\MSTART
- HKLM\System\CurrentControlSet\Services\MSTART\Security
- HKLM\System\CurrentControlSet\Services\Mseu
- HKLM\system\currentcontrolset\services\UnzipService
Sets these values:
- HKLM\System\CurrentControlSet\Services\EventLog\System\MSTART EventMessageFile = %SystemRoot%\System32\Drivers\MSTART.SYS;
- HKLM\System\CurrentControlSet\Services\EventLog\System\MSTART TypesSupported = 7
- HKLM\System\CurrentControlSet\Services\MSTARTType = 1 by %windir%\system32\services.exe (PID:640)
- HKLM\System\CurrentControlSet\Services\MSTART Start = 3
- HKLM\System\CurrentControlSet\Services\MSTART ErrorControl = 1
- HKLM\System\CurrentControlSet\Services\MSTART ImagePath = \??\C:\WINDOWS\system32\Drivers\MSTART.SYS [Launchpoint: Service]
- HKLM\System\CurrentControlSet\Services\MSTART DisplayName = MSTART
- HKLM\System\CurrentControlSet\Services\MSTART\Security Security = by %windir%\system32\services.exe (PID:640)
- HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Run [Launchpoint: Run]
- HKLM\System\CurrentControlSet\Services\Mseu Type = 1
- HKLM\System\CurrentControlSet\Services\Mseu Start = 2
- HKLM\System\CurrentControlSet\Services\Mseu ErrorControl = 1
- HKLM\System\CurrentControlSet\Services\Mseu Tag = 1
- HKLM\System\CurrentControlSet\Services\Mseu Group = Extended base
- HKLM\system\currentcontrolset\services\UnzipService Type = 272
- HKLM\system\currentcontrolset\services\UnzipService Start = 2 by %localsettings\Temp\Regini.exe (PID:428)
- HKLM\system\currentcontrolset\services\UnzipService by %localsettings\Temp\Regini.exe (PID:428) [Launchpoint: Service]
- HKLM\system\currentcontrolset\services\UnzipService ErrorControl = 0
- HKLM\system\currentcontrolset\services\UnzipService DisplayName = Self extract service
- HKLM\system\currentcontrolset\services\UnzipService ObjectName = LocalSystem
- HKLM\system\currentcontrolset\services\UnzipService
Description = Self extract archive decrypt
Infection
After a certain time period from the initial infection, the worm will infect removable drives inserted into the system by dropping a copy of itself named zipsetup.exe and an autorun.inf file as shown below:
[autorun] shellexecute=zipsetup.exe /H
Payload
After a further period of dormancy, the worm will trigger its payload, which will overwrite the Master Boot Record of available drives on the system, and effectively crippling the file system and rendering data on the disk inaccessible except with specialist tools. The following dialog box will be displayed:
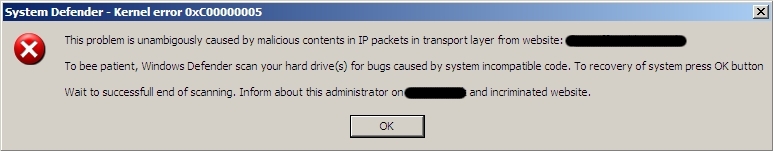
On reboot the system will be unbootable.
Removal
Manual removal:
1) Use task manager or process explorer to kill the "MSEUS.EXE" process.
2) Delete the following files:
- %windir%\system32\drivers\Mstart.sys
- %programfiles%\Dump\Dump.exe
- %windir%\system32\drivers\Mseu.sys
- %windir%\system32\mseus.exe
- %windir%\system32\tokset.dll
- %windir%\system32\ainf.inf
Delete as well any instances of zipsetup.exe on root folders as well as the autorun.inf
3) Delete the malicious registry entries, especially launchpoints as listed in the description.
4) Reboot system, run full scan.