Summary
Trojan:W32/Pakes.CSG attempts to get "rogueware" installed on the victim's computer by claiming the computer is infected by spyware. It also makes changes to the system registry and posts information about the computer to a remote server.
Removal
Based on the settings of your F-Secure security product, it will either move the file to the quarantine where it cannot spread or cause harm, or remove it.
A False Positive is when a file is incorrectly detected as harmful, usually because its code or behavior resembles known harmful programs. A False Positive will usually be fixed in a subsequent database update without any action needed on your part. If you wish, you may also:
Check for the latest database updates
First, check if your F-Secure security program is using the latest updates, then try scanning the file again.
Submit a sample
After checking, if you still believe the file is incorrectly detected, you can submit a sample of it for re-analysis.
Note: If the file was moved to quarantine, you need to collect the file from quarantine before you can submit it.
Exclude a file from further scanning
If you are certain that the file is safe and want to continue using it, you can exclude it from further scanning by the F-Secure security product.
Note: You need administrative rights to change the settings.
Technical Details
Pakes.CSG
Once executed the trojan copies itself to the following location:
- %windir%\system32\ctfmona.exe
It drops the following two files, a desktop wallpaper and a screensaver:
- %windir%\system32\ctfmonb.bmp
- %windir%\system32\blackster.scr
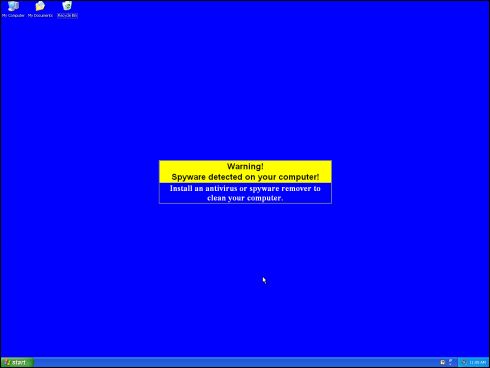
The ctfmonb.bmp file is set as the desktop wallpaper to warn the user of a non-existent spyware infection.
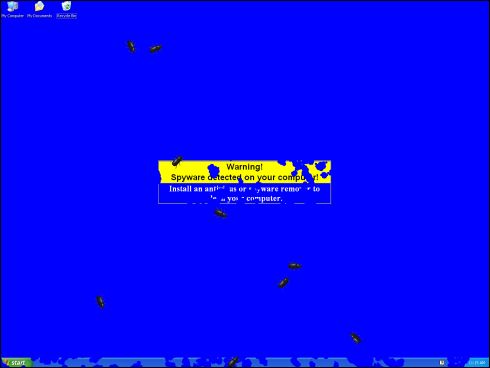
The file called blackster.scr is set as the system's screensaver. Once it activates, a legion of bugs appear to eat away the desktop. The screensaver appears to not have been made by authors of the trojan. The original version is available on the Internet as freeware.Therefore having a similar screensaver alone does not mean you have a trojan on your computer.
To enable its execution on start-up and to change the wallpaper and screensaver, the trojan makes several changes to the system registry. Trojan:W32/Pakes.CSG also disables System Restore with a registry modification.The following is a list of the registry changes made by Pakes.CSG:
- HKLM\Software\Microsoft\Software Notifier InstallationID = 30ca1f71-3146-4d7b-a35f-3736e1cd05bd
- HKCU\Control Panel\Colors Background = 0 0 255
- HKCU\Control Panel\Desktop WallpaperStyle = 0 [Wallpaper Changed]
- HKCU\Control Panel\Desktop TileWallpaper = 0
- HKCU\Control Panel\Desktop Wallpaper = C:\WINDOWS\system32\ctfmonb.bmp [Wallpaper Changed]
- HKCU\Control Panel\Desktop OriginalWallpaper = C:\WINDOWS\system32\ctfmonb.bmp
- HKCU\Control Panel\Desktop ConvertedWallpaper = C:\WINDOWS\system32\ctfmonb.bmp
- HKLM\Software\Microsoft\Windows\CurrentVersion\Run ctfmona = C:\WINDOWS\system32\ctfmona.exe [Launchpoint: Run]
- HKLM\System\CurrentControlSet\Services\srservice Start = 00000002
- HKLM\System\CurrentControlSet\Services\sr Start = 00000000
- HKLM\System\CurrentControlSet\Services\sr ImagePath = system32\DRIVERS\sr.sys [Launchpoint: Service]
- HKLM\Software\Microsoft\Windows NT\CurrentVersion\SystemRestore DisableSR = 00000000 [System Restore Disabled]
- HKCU\Control Panel\Desktop SCRNSAVE.EXE = C:\WINDOWS\system32\blackster.scr
Once running the trojan posts information to the following location:
- https://www.winifixer.com/log2.php
The information sent by the trojan includes hardware and Operating System information, installed software, and currently running processes.The trojan also attempts to connect to the following location:
- https://windowsupdate.microsoft.com/
Connecting to Windows Update tests if the computer has a working Internet connection. The trojan then attempts to download a file from:
- https://winifixer.com/banner2/1208441289/[Removed]/[Removed].gif
Rogue Antispyware
The goal of this trojan is to install and push the sale of a rogue application. Rogue applications produce fraudulent scan results and use affiliate programs to market themselves. Trojans such as Pakes.CSG are designed and used by unscrupulous affiliates.More details are available from the Rogue antispyware description.
Protect your devices from malware with F‑Secure Total
Protecting your devices from malicious software is essential for maintaining online security. F‑Secure Total makes this easy, helping you to secure your devices in a brilliantly simple way.
Award‑winning antivirus and malware protection
Online browsing, banking, and shopping protection
24/7 online identity and data breach monitoring
Unlimited VPN service to safeguard your privacy
Password manager with private data protection
Choose how many devices you want to protect to get started.
Free customer support
Cancel anytime
The trial does not obligate you to buy the product
After 30 days your subscription will renew automatically for one year at €69.99.
More Support
Community
Ask questions in our Community.
User guides
Check the user guide for instructions.
Contact Support
Chat with with or call an agent.
Submit a Sample
Submit a file or URL for analysis.


)
)