Email-Worm:W32/Mydoom.B
Summary
This type of worm is embedded in an email attachment, and spreads using the infected computer's emailing networks.
Removal
Based on the settings of your F-Secure security product, it will either move the file to the quarantine where it cannot spread or cause harm, or remove it.
Caution: Manual disinfection is a risky process; it is recommended only for advanced users.
Manual disinfection of Mydoom consists of the following steps:
-
Delete the registry value and restart the computer:
- [HKLM\Software\Microsoft\Windows\CurrentVersion\Run\Explorer]
- [HKCR\CLSID\{E6FB5E20-DE35-11CF-9C87-00AA005127ED}\InProcServer32]
-
Delete the worm from the Windows System Directory:
- %SysDir%\explorer.exe
-
and its backdoor component from:
- %SysDir%\ctfmon.dll
- To enable access again to the sites blocked by Mydoom.B, it is necessary to locate the file "hosts" and delete all the lines referring to Anti-Virus vendors and other commercial sites. The lines added by the worm are listed later in this page.
A False Positive is when a file is incorrectly detected as harmful, usually because its code or behavior resembles known harmful programs. A False Positive will usually be fixed in a subsequent database update without any action needed on your part. If you wish, you may also:
-
Check for the latest database updates
First check if your F-Secure security program is using the latest updates, then try scanning the file again.
-
Submit a sample
After checking, if you still believe the file is incorrectly detected, you can submit a sample of it for re-analysis.
Note: If the file was moved to quarantine, you need to collect the file from quarantine before you can submit it.
-
Exclude a file from further scanning
If you are certain that the file is safe and want to continue using it, you can exclude it from further scanning by the F-Secure security product.
Note: You need administrative rights to change the settings.
Technical Details
Email-Worm:W32/Mydoom.B is an email worm that is capable of launching attacks against two websites, www.sco.comand www.microsoft.com. The worm also prevents infected machines from accessing anti-virus sites, including www.f-secure.com.
Mydoom.B is a variant of the Mydoom worm. It uses the same scrambling technique as the previous variant, ROT13, and shares most of its features. The worm contains this message, which is never displayed:
- (sync-1.01; andy; I'm just doing my job, nothing personal, sorry)
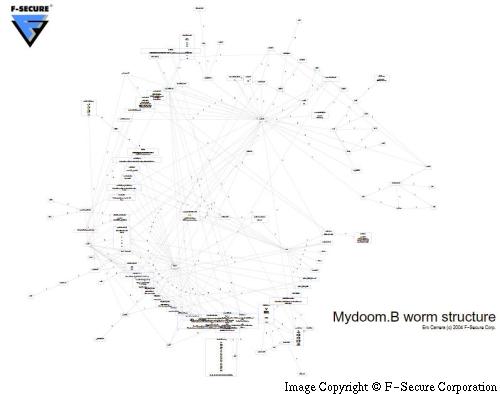
The following picture briefly shows the structure of the Mydoom.B worm, which can be appreciated in full detail in the PDF graph available here.
Mydoom.B, was found spreading on January 28th, 2005. The worm has a limited lifespan: it is coded to exit immediately when run after 1st of March 2004 at 03:18:42 (UTC)
Installation
It will copy itself to the following location:
- %sysDir%\explorer.exe
And will add the following registry entries:
- [HKLM\Software\Microsoft\Windows\CurrentVersion\Run] "Explorer" = %sysdir%\explorer.exe
or, if it fails:
- [HKCU\Software\Microsoft\Windows\CurrentVersion\Run] "Explorer" = %sysdir%\explorer.exe
It drops its backdoor component, encoded in its body and packed with UPX as:
- %sysdir%\ctfmon.dll
This is loaded under Explorer from this registry key:
- [HKEY_CLASSES_ROOT\CLSID\{E6FB5E20-DE35-11CF-9C87-00AA005127ED}\InProcServer32]
The worm will create a mutex with the name "sync-v1.01__ipcmtx0" to ensure only one instance of itself is running at the same time.
Activity
Once run it will look for the previous variant, Mydoom.A, and will terminate its process and delete "shimgapi.dll".
The worm has the ability of sending itself to already infected computers. It will do so by first finding them through a network scan, where IP addresses will be randomly forged (skipping some invalid ranges). Then a connection attempt is made to port 3127 (opened by previous variant's backdoor), if the machine is found infected then the worm transfers itself and will be executed immediately, thereby updating the infected computers to the new version without the need for the user to receive the worm through email.
Additionally, the worm will request the infected computer's hostname through gethostbyname(), resolve its IP and scan for other infected computers in the same range.
The worm will perform a Distributed Denial of Service (DDoS) attack against www.microsoft.com on 3rd of February 2004 at 13:09:18 (UTC) and www.sco.com on 1st of February 2004 at 16:09:18 (UTC).
The DDoS attack launches 8 threads against www.sco.comevery 1024 milliseconds.
The other DDoS attack launches 14 threads against www.microsoft.com every 1024 milliseconds.
The hosts file in the infected machines will be modified so that domains belonging to Anti-Virus companies and other commercial sites are resolved to the IP address 0.0.0.0, rendering them inaccessible. The file is encrypted within the worms code and contain the following:
- 0.0.0.0 engine.awaps.net awaps.net www.awaps.net ad.doubleclick.net
- 0.0.0.0 spd.atdmt.com atdmt.com click.atdmt.com clicks.atdmt.com
- 0.0.0.0 media.fastclick.net fastclick.net www.fastclick.net ad.fastclick.net
- 0.0.0.0 ads.fastclick.net banner.fastclick.net banners.fastclick.net
- 0.0.0.0 www.sophos.com sophos.com ftp.sophos.com f-secure.com www.f-secure.com
- 0.0.0.0 ftp.f-secure.com securityresponse.symantec.com
- 0.0.0.0 www.symantec.com symantec.com service1.symantec.com
- 0.0.0.0 liveupdate.symantec.com update.symantec.com updates.symantec.com
- 0.0.0.0 support.microsoft.com downloads.microsoft.com
- 0.0.0.0 download.microsoft.com windowsupdate.microsoft.com
- 0.0.0.0 office.microsoft.com msdn.microsoft.com go.microsoft.com
- 0.0.0.0 nai.com www.nai.com vil.nai.com secure.nai.com www.networkassociates.com
- 0.0.0.0 networkassociates.com avp.ru www.avp.ru www.kaspersky.ru
- 0.0.0.0 www.viruslist.ru viruslist.ru avp.ch www.avp.ch www.avp.com
- 0.0.0.0 avp.com us.mcafee.com mcafee.com www.mcafee.com dispatch.mcafee.com
- 0.0.0.0 download.mcafee.com mast.mcafee.com www.trendmicro.com
- 0.0.0.0 www3.ca.com ca.com www.ca.com www.my-etrust.com
- 0.0.0.0 my-etrust.com ar.atwola.com phx.corporate-ir.net
An additional line is added before the the date when attack against Microsoft begins:
- 0.0.0.0 www.microsoft.com
Which will make the site inaccessible. The 3rd of February the entry will be removed so the attack can be performed, which will probably cause some difficulties reaching it, if the DDoS is successful.
The modifications in the hosts file are probably targeted so that customers of the most widespread Anti-Virus products can't download new updates to disinfect the worm.
Propagation (Peer-to-Peer)
The following filenames are used in this variant when copying itself to Kazaa
- NessusScan_pro
- attackXP-1.26
- winamp5
- MS04-01_hotfix
- zapSetup_40_148
- BlackIce_Firewall_Enterpriseactivation_crack
- xsharez_scanner
- icq2004-final
And extensions chosen from:
- .bat
- .exe
- .scr
- .pif
Propagation (email)
The email messages sent by the worm have the following characteristics: Subjects can be any of the following:
- Status
- hi
- Delivery Error
- Mail Delivery System
- hello
- Error
- Server Report
- Returned mail
The body text can be one of the following:
- The message cannot be represented in 7-bit ASCII encoding and has been sent as a binary attachment.
- sendmail daemon reported: Error #804 occured during SMTP session. Partial message has been received.
- The message contains Unicode characters and has been sent as a binary attachment.
- The message contains MIME-encoded graphics and has been sent as a binary attachment.
- Mail transaction failed. Partial message is available.
Attachments are composed combining the following names:
- document
- readme
- doc
- text
- file
- data
- message
- body
with the following extensions:
- pif
- scr
- exe
- cmd
- bat
As with older Mydoom variants, Mydoom.B collects addresses from Windows' Address Book and from files with extension:
- wab
- pl
- adb
- dbx
- asp
- php
- sht
- htm
- txt
It will try to avoid anti-spam tricks used by people to obfuscate emails addresses in webpages.
Once an address is chosen from the list of harvested addresses, the worm will send an email to addresses in the same domain but to accounts like:
- john
- alex
- michael
- james
- mike
- kevin
- david
- george
- sam
- andrew
- jose
- leo
- maria
- jim
- brian
- serg
- mary
- ray
- tom
- peter
- robert
- bob
- jane
- joe
- dan
- dave
- matt
- steve
- smith
- stan
- bill
- bob
- jack
- fred
- ted
- adam
- brent
- alice
- anna
- brenda
- claudia
- debby
- helen
- jerry
- jimmy
- julie
- linda
- sandra
It will avoid sending itself to email addresses containing the following account names:
- root
- info
- samples
- support
- postmaster
- webmaster
- noone
- nobody
- nothing
- anyone
- someone
- your
- you
- me
- bugs
- rating
- site
- contact
- soft
- no
- somebody
- privacy
- service
- help
- not
- submit
- feste
- ca
- gold-certs
- the.bat
- page