Technical Details
Bluetooth-Worm:SymbOS/Lasco.A is distributed in a SIS file named velasco.sis.
The velasco.sis file will not arrive automatically to the target device, so user needs to answer yes to the transfer question while the infected device is still in range. This modification in the replication mechanism, will make it more likely that Lasco.A will spread quickly once in the wild.
Lasco worm can reach only mobile phones that support Bluetooth and are in discoverable mode. Setting your phone into non-discoverable (hidden) Bluetooth mode will protect your phone. But once the phone is infected, it will try to infect other systems even if the user tries to disable Bluetooth from system settings.
Distribution
When the Lasco.A worm is activated it will start looking for other bluetooth devices, and starts sending infected velasco.sis files to the first device it finds. After the first target phone is out of range the Lasco.A will continue searching and infecting other phones.
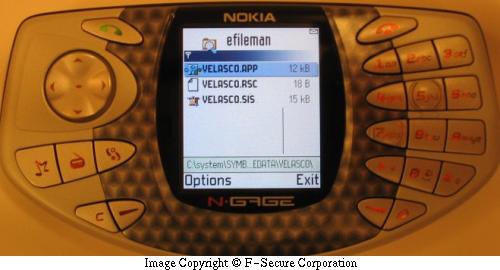
The SIS file contains the worm's main executable files:
- velasco.app
- marcos.mdl - system recognizer
- velasco.rsc - resource file
The file also contains autostart settings that will automatically execute velasco.app after the SIS file is being installed.
Installation
When the velasco.sis file is installed the installer will copy the worm executables into following locations:
- c:\system\apps\velasco\velasco.rsc
- c:\system\apps\velasco\velasco.app
- c:\system\apps\velasco\flo.mdl
When the velasco.app is executed it copies the following files:
- flo.mdl to c:\system\recogs
- velasco.app to c:\system\symbiansecuredata\velasco\
- velasco.rsc to c:\system\symbiansecuredata\velasco\
This is most likely done in case user installs the application to memory card, or to avoid user trying to disinfect the worm by uninstalling the original SIS file.
Then the worm will recreate the velasco.sis file from worm component files and data blocks that are in velasco.app.
After recreating the SIS file the Lasco.A will search for all SIS files in the device, add itself into those files and modify the SIS file header so that the Lasco.A embedded into target SIS files will activate automatically upon install of that SIS file into the device.
Infection
Lasco.A also replicates by searching the infected device for all SIS installation files. And infecting them by adding the velasco.sis installation file as last file in the SIS archive.
The Lasco.A will also modify the infected SIS file header so that the embedded velasco SIS installation will start automatically after the host SIS file is installed. But while the Lasco.A is installation is started automatically, the installation sequence will still be normal and use will be asked whether he wants to install Velasco, and user will get warning about missing signature in the SIS file.