Summary
Worm:W32/BadTrans is a worm spreading with email messages from Win32 systems. The worm sends email messages with infected attached files, as well as installs a spying trojan component to steal information from infected systems. The worm was discovered in-the-wild on April 12 2001.
Removal
Based on the settings of your F-Secure security product, it will either move the file to the quarantine where it cannot spread or cause harm, or remove it.
A False Positive is when a file is incorrectly detected as harmful, usually because its code or behavior resembles known harmful programs. A False Positive will usually be fixed in a subsequent database update without any action needed on your part. If you wish, you may also:
Check for the latest database updates
First, check if your F-Secure security program is using the latest updates, then try scanning the file again.
Submit a sample
After checking, if you still believe the file is incorrectly detected, you can submit a sample of it for re-analysis.
Note: If the file was moved to quarantine, you need to collect the file from quarantine before you can submit it.
Exclude a file from further scanning
If you are certain that the file is safe and want to continue using it, you can exclude it from further scanning by the F-Secure security product.
Note: You need administrative rights to change the settings.
Technical Details
The worm itself is Win32 executable file (PE EXE file). It was found in-the-wild in a compressed form, and is about 13Kb long. Being decompressed the worm's file length increases to about 40Kb.
Installation
The worm has a multi-component structure. It consists of two different components that are dropped on a hard disk as three different files and are run as stand-alone programs (email Worm and Trojan). The worm routine is the main component, it keeps trojan program body in its code and installs it into a system while infecting a new machine.
The worm component operates similar to I-Worm.ZippedFiles (aka ExploreZip) worm: by using Windows MAPI functions it gets access to Inbox and "answers" all unread messages. This routine has a bug and may cause transport overload (see below).
The trojan component itself is a variant of already known passwords-stealing trojan (see Trojan.PSW.Hooker). It sends information from infected computers to the email address:
- ld8dl1@mailandnews.com
When an infected file is run (when a user clicks on attached file and activates it) the worm code gets control. First of all it drops (installs) its components to the system. The worm copies itself to Windows directory with INETD.EXE name and drops the trojan component to Windows directory with HKK32.EXE name. The trojan component is executed then, it moves itself to Windows system directory with KERN32.EXE name, drops an additional library (key logger) with HKSDLL.DLL name. The worm then registers itself (the INETD.EXE file) in auto-run sections in the system. Under Win9x it writes "run=" command to [windows] section to WIN.INI file, for example:
- [windows] load= run=C:\WINDOWS\INETD.EXE
Under WinNT/2000 the following registry key is created:
- HKCU\Software\Microsoft\Windows NT\CurrentVersion\Windows RUN = C:\WINDOWS\INETD.EXE
The trojan registers itself in the Registry in RunOnce key:
- HKLM\Software\Microsoft\Windows\CurrentVersion\RunOnce kernel32 = kern32.exe
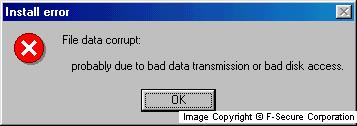
Because this is "run once" key, the trojan on each start rewrites it, and keeps Windows loading trojan file on each restart. To hide its activity when installation into a new machine is complete the worm displays the fake message and exits:
- Install error
- File data corrupt:
- probably due to bad data transmission or bad disk access.
The message looks like:
The worm does not send any messages out of infected machine at first start, it does that on next Windows restarts instead. The spreading routine is activated on next Windows restart when the worm copy is activated from INETD.EXE file (this file is run automatically because it is referred from "run" key in WIN.INI file or system registry). The worm registers itself as hidden (service) process, and sleeps for about 5 minutes before activating its spreading routine.
Propagation (email)
While spreading the worm gets access to Windows MAPI functions, opens and reads all unread messages, "answers" on them with infected messages. The worm does not terminate, and is active till Windows restart, and sends infected message each time a new message arrives. The infected message has text and attached file. Attached file name is randomly selected from the following variants:
- Pics.ZIP.scr
- images.pif
- README.TXT.pif
- New_Napster_Site.DOC.scr
- news_doc.scr
- hamster.ZIP.scr
- YOU_are_FAT!.TXT.pif
- searchURL.scr
- SETUP.pif
- Card.pif
- Me_nude.AVI.pif
- Sorry_about_yesterday.DOC.pif
- s3msong.MP3.pif
- docs.scr
- Humor.TXT.pif
- fun.pif
The Subject field in worm messages is the same as in original message with prepended "Re:" prefix. The message body is a "reply" to the original message. For example, if original message is sent from "John Doe" and has two lines like:
- message line1
- message line2
the worm will reply with the following text then:
'John Doe' wrote: ==== - message line1 - message line2 > Take a look to the attachment.
If a message has no body (empty message), the worm's "reply" has just one line:
- > Take a look to the attachment.
The worm uses a trick to avoid answering the same email twice or more times, and to avoid answering its own messages received from other infected machines. To do that the worm adds two spaces to the end of Subject line, and does not process (reply to) such messages. This "two-spaces" protection works for messages that are already "answered", and worm does not reply to these messages. However, this protection doesn't work for messages that are received from other infected computers. Some email servers (or most of them) simply cut all spaces at the end of Subject line (according to RFC-822 email messages standard).
As a result if an infected message comes to already infected machine it is immediately answered by worm and sent back. So the worm initiates the "looped" traffic with endless number of infected messages. Depending on installed email client the worm also fails to mark "answered" messages.
As a result the worm answers all unread messages ("true" ones and its own messages) in endless loop, and number of sent and received messages grows up to several thousand within a minute. Therefore, the worm can cause email server crash because soon it will not be capable to process all these messages.
Protect your devices from malware with F‑Secure Total
Protecting your devices from malicious software is essential for maintaining online security. F‑Secure Total makes this easy, helping you to secure your devices in a brilliantly simple way.
Award‑winning antivirus and malware protection
Online browsing, banking, and shopping protection
24/7 online identity and data breach monitoring
Unlimited VPN service to safeguard your privacy
Password manager with private data protection
Choose how many devices you want to protect to get started.
Free customer support
Cancel anytime
The trial does not obligate you to buy the product
After 30 days your subscription will renew automatically for one year at €69.99.
More Support
Community
Ask questions in our Community.
User guides
Check the user guide for instructions.
Contact Support
Chat with with or call an agent.
Submit a Sample
Submit a file or URL for analysis.


)
)