Rogue:W32/AntiSpySpider
Summary
Dishonest antivirus software which tricks users into buying or installing it, usually by infecting a user's computer, or by pretending the computer is infected.
Removal
Based on the settings of your F-Secure security product, it may block the file from running, move it to the quarantine where it cannot spread or cause harm, or ask you to select an action.
A False Positive is when a file is incorrectly detected as harmful, usually because its code or behavior resembles known harmful programs. A False Positive will usually be fixed in a subsequent database update without any action needed on your part. If you wish, you may also:
-
Check for the latest database updates
First check if your F-Secure security program is using the latest updates, then try scanning the file again.
-
Submit a sample
After checking, if you still believe the file is incorrectly detected, you can submit a sample of it for re-analysis.
Note: If the file was moved to quarantine, you need to collect the file from quarantine before you can submit it.
-
Exclude a file from further scanning
If you are certain that the file is safe and want to continue using it, you can exclude it from further scanning by the F-Secure security product.
Note: You need administrative rights to change the settings.
Technical Details
This is the detection for the rogue antispyware program AntiSpySpider, and the downloaders it installs on the infected system.
The presence of this rogue on a system is characterized by the presence of these files:
- C:\WINDOWS\system32\sft.res
- C:\WINDOWS\system32\sockins32.dll
- C:\WINDOWS\system32\sockots64.dll
And these registry entries:
- HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{66186F05-BBBB-4a39-864F-72D84615C679}
- HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{66186F05-BBBB-4a39-864F-72D84615C679}\InProcServer32& @ = "sockins32.dll"& ThreadingModel = "Apartment"
- HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{FFFFFFFF-BBBB-4146-86FD-A722E8AB3489}&&& &&& @ = "Microsoft copyright"
- HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{FFFFFFFF-BBBB-4146-86FD-A722E8AB3489}\InprocServer32& @ = "sockins32.dll"& ThreadingModel = "Apartment"
- HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Active Setup\Installed Components\{66186F05-BBBB-4a39-864F-72D84615C679}&&& @&&& "Systray component"& Locale = "EN"& StubPath = "rundll32 sockins32.dll,InitModule"& IsInstalled = dword:00000001& Version = "1,0,0,2"
- HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Browser Helper Objects\{FFFFFFFF-BBBB-4146-86FD-A722E8AB3489}&&& &&&
- HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\ShellServiceObjectDelayLoad& WebProxy = "{66186F05-BBBB-4a39-864F-72D84615C679}"
- HKEY_LOCAL_MACHINE\SOFTWARE\TSoft&&& &&&
Activity
The malware will attempt to retrieve information from the following locations:
- https://spiderfront.net
- https://digitaltreath.info
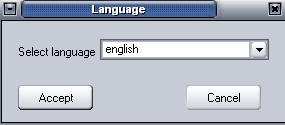
When the malware is in the system the installation process begins with this screen:
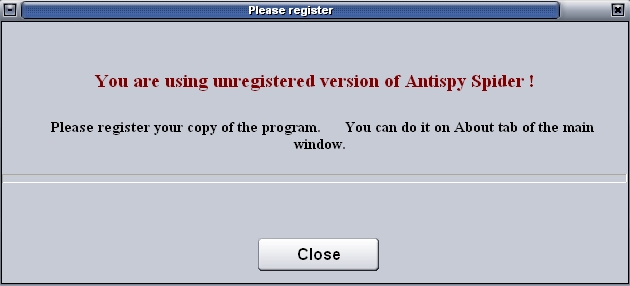
After installation, the following "registration request" message appears:
Then this screen will show:
.jpg)
If you click the "Scan" button, the program will report that your system has a lot of infections, but it shows no breakdown of the infections:
.jpg)
And it will report these infections even if the system is clean to dupe the user into purchasing the registered version.