Summary
At the time of writing, F-Secure has received no report about this worm from the field.
Gigger is a destructive worm that spreads itself as a fast mass-mailer by using Outlook and as a slow mass-mailer (in infected HTML messages) using Outlook Express. It is written in both JavaScript and Visual Basic Script.
Removal
Based on the settings of your F-Secure security product, it will either move the file to the quarantine where it cannot spread or cause harm, or remove it.
A False Positive is when a file is incorrectly detected as harmful, usually because its code or behavior resembles known harmful programs. A False Positive will usually be fixed in a subsequent database update without any action needed on your part. If you wish, you may also:
Check for the latest database updates
First, check if your F-Secure security program is using the latest updates, then try scanning the file again.
Submit a sample
After checking, if you still believe the file is incorrectly detected, you can submit a sample of it for re-analysis.
Note: If the file was moved to quarantine, you need to collect the file from quarantine before you can submit it.
Exclude a file from further scanning
If you are certain that the file is safe and want to continue using it, you can exclude it from further scanning by the F-Secure security product.
Note: You need administrative rights to change the settings.
Technical Details
Variant:Gigger.A (Gigger.A@mm, JS_GIGGER.A,JS/Gigger.a@MM, JS.Gigger.A, JS/Gigger-A)
When executed, the worm first creates two files into the root of the C: drive: "b.htm" and "bla.hta".
Next Gigger checks an infection marker from the registry, and if it is not present, it is created. The registry key is:
HKEY_CURRENT_USER\Software\TheGrave\badUsers\v2.0
The worm goes all mapped network drives from "C" to "M". If possible, it creates a copy of itself into file
\windows\start menu\programs\startup\msoe.hta
for each drive. It also copies itself to
"Windows\Help\mmsn_offline.htm" and "Windows\Samples\WSH\chart.js".
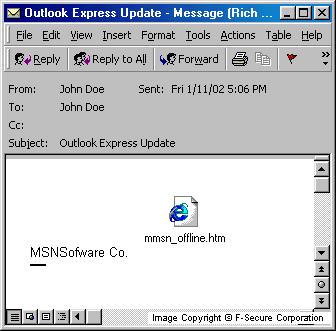
Spreading via Outlook Express
The worm executes its slow mass-mailing routine. It changes Outlook Express settings so that every message sent from an infected machine is in HTML format and contains a copy of the worm, by embedding the file "mmsn_offline.htm" into the message. On that way the worm will activate when next recipient open or view such infected message.
Spreading via Outlook
The fast mass mailing part of the worm collects email addresses from both Outlook contacts folder and from the Windows Address Book. The worm sends itself to each address collected with the following characteristics:
Subject: Outlook Express Update Body: MSNSoftware Co. Attachment: mmsn_offline.htm
The worm also sends a message to g_dv20@mail.bg, which propably belongs to the virus writer. The message contains a list of all email addresses where the worm was sent.
If the worm fails in the above section to access Outlook, or it fails to create files that it needs, it adds a line to the "c:\autoexec.bat" that attempts to format the C: drive. However, this payload is able to activate only in Windows 9x, and it may not work in localized versions.
The JavaScript code contains the following comment:
//29.10.2001, 10/29/01 This worm is donation from all Bulgarians!CopyR2001McB
Gigger also drops "Windows\Help\Charts.vbs", which contains another fast mass-mailer, and runs it. It also adds it to the registry, so it will be executed in the each system startup by using the following registry key:
HKLM\Software\Microsoft\Windows\CurrentVersion\Run\NAV DefAlert
The worm again collects email addresses from Outlook Contacts folder, and sends the following message to each recipient:
Subject: (email address of the recipient) Body: Microsoft Outlook 98 Attachment: mmsn_offline.htm
The attachment name is set to "Reports", which is the reason why some email clients may show the attachment as "Reports" instead of "mmsn_offline.htm".
The worm also goes through all hard and mapped network drives, appending the worm code to each file that has extension ".htm", ".html" or ".asp".
Further, if the directory contains any files with either ".ini" or ".hlp" extensions, a file "script.ini" is created as well. Therefore, if the user has IRC client mIRC installed into system, the worm will replace the default "script.ini" with its own. After that the worm sends itself to each user that joins the same IRC channel where the infected user is.
If the day of the month is 1st, 5th, 10th, 15th or 20th, the worm replaces all files from all drives with a zero byte files, destroying their original content.
F-Secure Anti Virus detects Gigger worm by heuristics and generic detection.
Protect your devices from malware with F‑Secure Total
Protecting your devices from malicious software is essential for maintaining online security. F‑Secure Total makes this easy, helping you to secure your devices in a brilliantly simple way.
Award‑winning antivirus and malware protection
Online browsing, banking, and shopping protection
24/7 online identity and data breach monitoring
Unlimited VPN service to safeguard your privacy
Password manager with private data protection
Choose how many devices you want to protect to get started.
Free customer support
Cancel anytime
The trial does not obligate you to buy the product
After 30 days your subscription will renew automatically for one year at €69.99.
More Support
Community
Ask questions in our Community.
User guides
Check the user guide for instructions.
Contact Support
Chat with with or call an agent.
Submit a Sample
Submit a file or URL for analysis.


)
)