Summary
Gibe is a mass-mailing worm written in Visual Basic. It disguises itself as a Microsoft security update.
Removal
Based on the settings of your F-Secure security product, it will either move the file to the quarantine where it cannot spread or cause harm, or remove it.
A False Positive is when a file is incorrectly detected as harmful, usually because its code or behavior resembles known harmful programs. A False Positive will usually be fixed in a subsequent database update without any action needed on your part. If you wish, you may also:
Check for the latest database updates
First, check if your F-Secure security program is using the latest updates, then try scanning the file again.
Submit a sample
After checking, if you still believe the file is incorrectly detected, you can submit a sample of it for re-analysis.
Note: If the file was moved to quarantine, you need to collect the file from quarantine before you can submit it.
Exclude a file from further scanning
If you are certain that the file is safe and want to continue using it, you can exclude it from further scanning by the F-Secure security product.
Note: You need administrative rights to change the settings.
Technical Details
The worm usually arrives as an attachment named Q216309.exe to the following message:
From: Microsoft Corporation Security Center mailto:rdquest12@microsoft.com] To: Microsoft Customer Subject: Internet Security Update Attachment: q216309.exe Microsoft Customer, this is the latest version of security update, the update which eliminates all known security vulnerabilities affecting Internet Explorer and MS Outlook/Express as well as six new vulnerabilities, and is discussed in Microsoft Security Bulletin MS02-005. Install now to protect your computer from these vulnerabilities, the most serious of which could allow an attacker to run code on your computer. Description of several well-know vulnerabilities: - "Incorrect MIME Header Can Cause IE to Execute email Attachment" vulnerability. If a malicious user sends an affected HTML email or hosts an affected email on a Web site, and a user opens the email or visits the Web site, Internet Explorer automatically runs the executable on the user's computer. - A vulnerability that could allow an unauthorized user to learn the location of cached content on your computer. This could enable the unauthorized user to launch compiled HTML Help (.chm) files that contain shortcuts to executables, thereby enabling the unauthorized user to run the executables on your computer. - A new variant of the "Frame Domain Verification" vulnerability could enable a malicious Web site operator to open two browser windows, one in the Web site's domain and the other on your local file system, and to pass information from your computer to the Web site. - CLSID extension vulnerability. Attachments which end with a CLSID file extension do not show the actual full extension of the file when saved and viewed with Windows Explorer. This allows dangerous file types to look as though they are simple, harmless files - such as JPG or WAV files - that do not need to be blocked. System requirements: Versions of Windows no earlier than Windows 95. This update applies to: Versions of Internet Explorer no earlier than 4.01 Versions of MS Outlook no earlier than 8.00 Versions of MS Outlook Express no earlier than 4.01 How to install Run attached file q216309.exe How to use You don't need to do anything after installing this item. For more information about these issues, read Microsoft Security Bulletin MS02-005, or visit link below. http://www.microsoft.com/windows/ie/downloads/critical/default.asp If you have some questions about this article contact us at rdquest12@microsoft.com Thank you for using Microsoft products. With friendly greetings, MS Internet Security Center. ---------------------------------------- ---------------------------------------- Microsoft is registered trademark of Microsoft Corporation. Windows and Outlook are trademarks of Microsoft Corporation.
It should be noted that due to bugs in worm's code this message might not be fully visible when it arrives on a recepient's system.
The body of the message describes a Microsoft vulnerability and tries to make the recipient click on the attached file.
This worm's file is 122880 bytes long and it is a dropper for several worm components. Being run, the worm's dropper outputs a dialog box asking a user if he wants to install a security update.
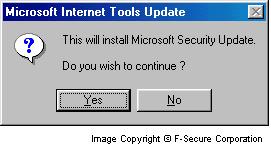
If a user clicks 'Yes', the worm shows the unpacking dialog with progress bar and in the end opens a messagebox informing that the update has been installed.

If a user clicks 'No' the worm installs itself too, but doesn't show any dialog or messageboxes.
The worm sets an infection marker so if it is run on an already infected system, then it shows the following message:
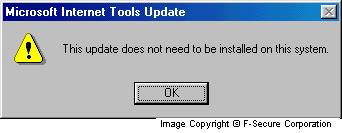
The following entry in the Registry is used as infection marker:
[HKEY_LOCAL_MACHINE\Software\AVTech\Settings] "Installed" = "... by Begbie"
When run, the worm drops several files to a system:
\%WinDir%\Q216309.exe - a copy of a dropper \%WinDir%\BcTool.exe - the mass-mailing component \%WinDir%\WinNetw.exe - email address searching component \%WinDir%\GfxAcc.exe - backdoor component \%WinSysDir%\Vtnmsccd.dll - a copy of a dropper \%WinSysDir%\MSWinsck.ocx - standard Winsock library
where \%WinDir%\ is Windows root directory and \%WinSysDir%\ is Windows System directory.
The email address searching component also creates a file with the name 02_N803.dat in Windows directory and stores all found email addresses there. This file is then loaded by the main mass-mailing component and the worm sends itself to all found email addresses.
The worm adds startup strings for its mass-mailing and backdoor components to the Registry. The following keys are created:
[HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run] "3DfxAcc" = "\%WinDir%\GfxAcc.exe" "LoadDBackUp" = "\%WinDir%\BcTool.exe"
where \%WinDir%\ is Windows root directory. This way both components are started during every Windows session.
To get rid of the worm it's enough to delete all its components from an infected system. If some components are locked while Windows is active, they have to be deleted from pure DOS (in case of Windows 9x system) or renamed with a different extension (EXA for example) with immediate system restart (in case of NT-based system). After restart the renamed components can be deleted.
Detection of Gibe worm was added into F-Secure Anti-Virus updates published on 6th of March 2002.
Protect your devices from malware with F‑Secure Total
Protecting your devices from malicious software is essential for maintaining online security. F‑Secure Total makes this easy, helping you to secure your devices in a brilliantly simple way.
Award‑winning antivirus and malware protection
Online browsing, banking, and shopping protection
24/7 online identity and data breach monitoring
Unlimited VPN service to safeguard your privacy
Password manager with private data protection
Choose how many devices you want to protect to get started.
Free customer support
Cancel anytime
The trial does not obligate you to buy the product
After 30 days your subscription will renew automatically for one year at €69.99.
More Support
Community
Ask questions in our Community.
User guides
Check the user guide for instructions.
Contact Support
Chat with with or call an agent.
Submit a Sample
Submit a file or URL for analysis.


)
)